

Safeguarding sensitive data and systems is paramount, yet conventional approaches often fall short. These methods rely on disparate tools and tactics, creating what we call ‘cybersecurity...

Data is the lifeblood of modern businesses that enables organizations to drive innovation. However, with the increasing reliance on data comes the need to protect it...


This embrace of hybrid cloud is happening industry wide at an impressive clip, according to Veeam vice president of enterprise strategy Dave Russell. “In recent years,...


Even in today’s 2D version of the internet, digital identity is a complicated affair. Phishing has become so sophisticated that an email from your bank, a...


Greater transmissibility means greater transmissibility in any setting, indoors or outdoors—even if outside is still safer Read More


“You know, it’s embarrassing,” well-known crypto podcaster Scott Melker tells Fortune. “I’m a person who talks about risk management and protecting your assets, but I was...

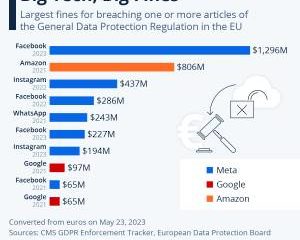
Thank you for joining us on “The cloud hub: From cloud chaos to clarity.” Increasingly, countries across the globe are enforcing data protection laws. Organizations can...


Celsius styles itself as a crypto alternative to traditional banks. That may not turn out so well for its users. Read More


An unidentified person allegedly broke into her apartment building and rang the doorbell to ask if Do Kwon was home. Read More


“It’s a double-edged sword,” says Bill Marczak, a senior researcher at the cybersecurity watchdog Citizen Lab. “You’re going to keep out a lot of the riffraff...